How Live Scan Works:
From Click to Fix.
The entire flow — trigger, scan, review, fix, accept — takes place inside VS Code without touching a browser or switching tools.
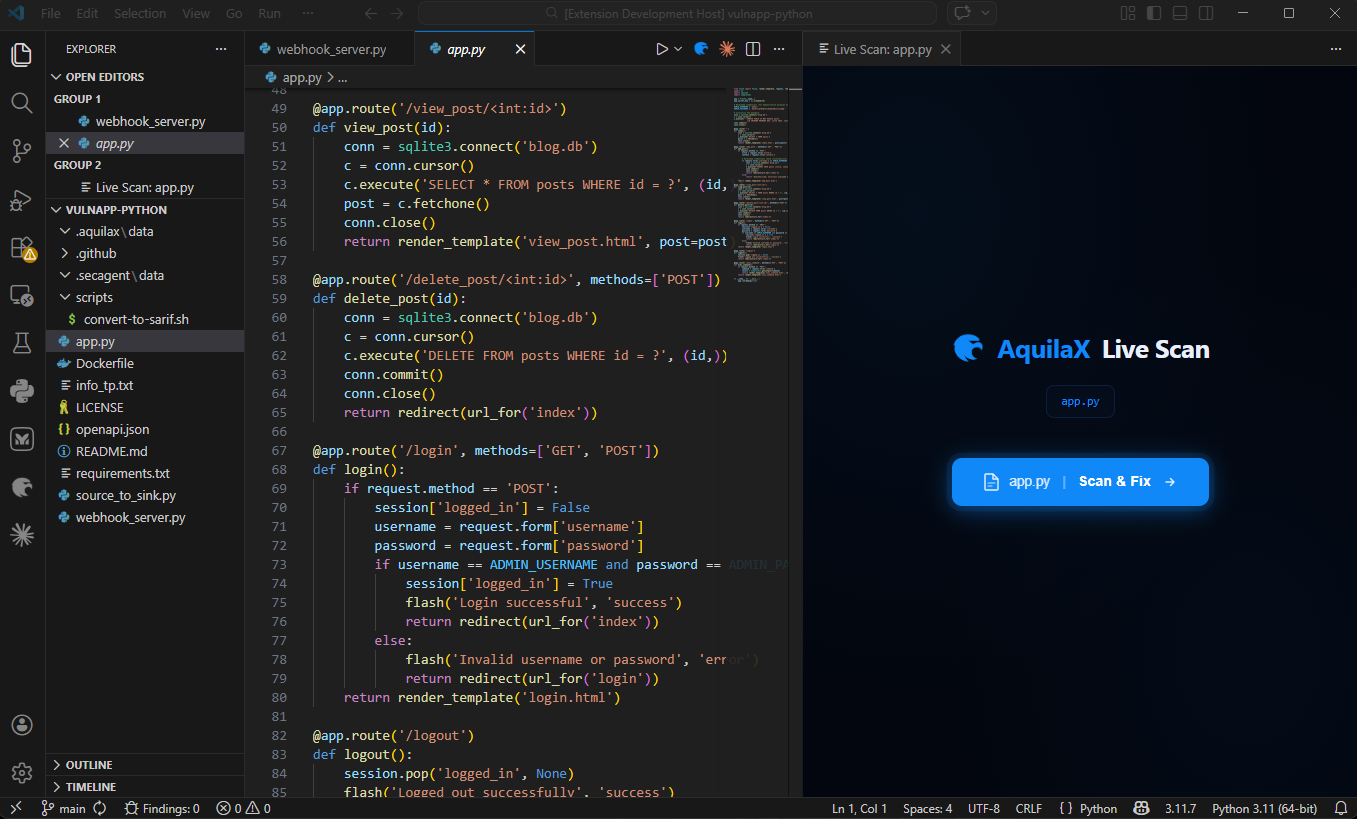
Click the AquilaX Scan Icon
A dedicated AquilaX scan icon appears in the top-right corner of the VS Code editor title bar whenever a file is open. Clicking it opens the Live Scan panel and immediately begins scanning the active file.
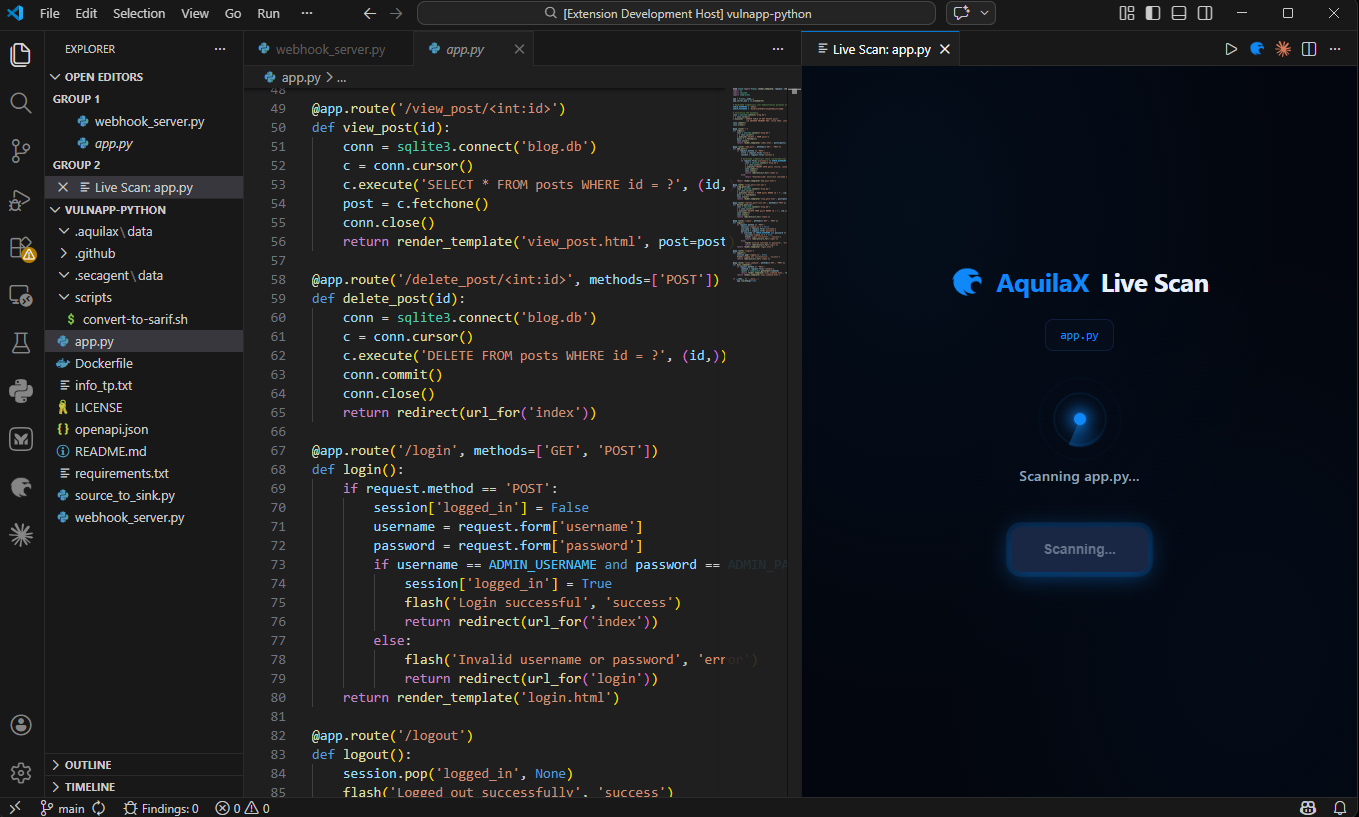
File Analysis Begins
The extension sends the current file's code to the AquilaX security engine, which analyses it against a comprehensive ruleset covering OWASP Top 10 vulnerabilities, CWE classifications, and language-specific security patterns.
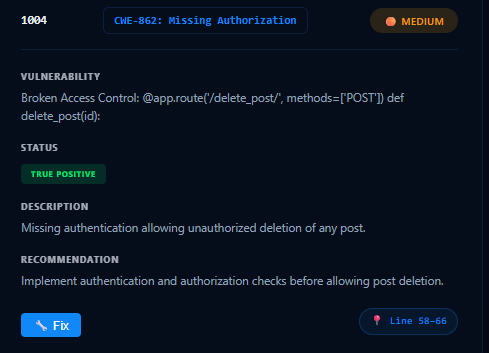
Review the Finding Cards
Once complete, the panel displays a list of finding cards — one per detected vulnerability. Each card shows the Rule ID, CWE badge, severity badge (CRITICAL / HIGH / MEDIUM / LOW), vulnerability type, verification status, description, recommendation, and the exact line number in the file.
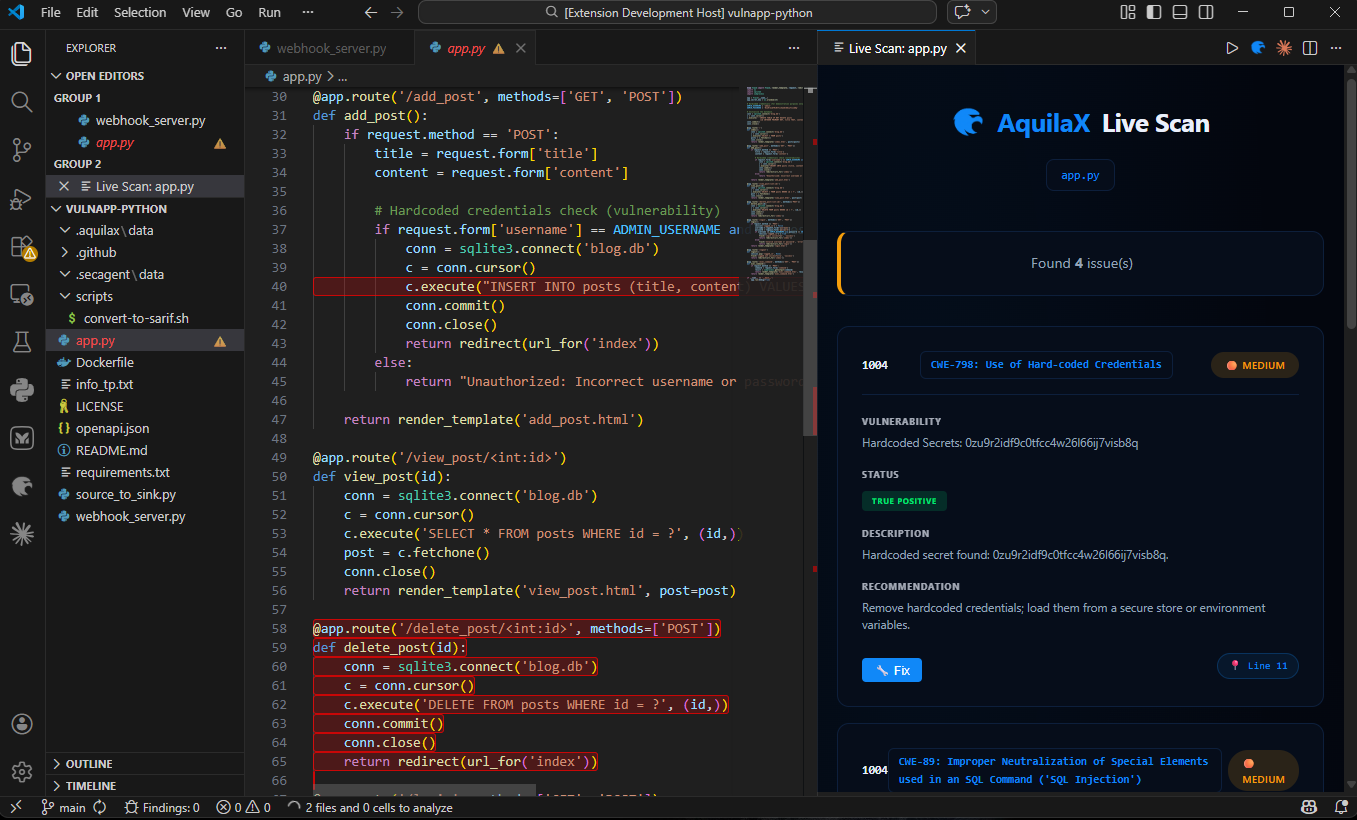
Navigate to the Vulnerable Line
Clicking anywhere on a finding card (outside the action buttons) jumps to the vulnerable line in the editor and highlights it, making it immediately visible in context. This helps developers understand exactly what code is problematic before applying any fix.
Trigger the AI Auto-Fix
Each finding card includes a Fix button. Clicking it triggers the AI auto-fix engine. The extension collects the vulnerable code along with surrounding context (10 lines above and below), detects the file's programming language automatically, and constructs a security-focused AI prompt including the vulnerability type, CWE, impact, and strict guardrails.
Context Collection
10 lines above and below the vulnerable code are collected to give the AI full function-level context.
Language Detection
The file's programming language is detected automatically — no manual configuration needed.
Prompt Construction
A security-focused prompt is built with the vulnerability type, CWE, impact, and strict guardrails to ensure a safe fix.
AI Fix Request
The request is sent to the AquilaX AI service. While generating, an animated "AI is fixing..." indicator is shown on the card.
Fix Applied
The corrected code is automatically applied to the file and the changed lines are highlighted in green for review.
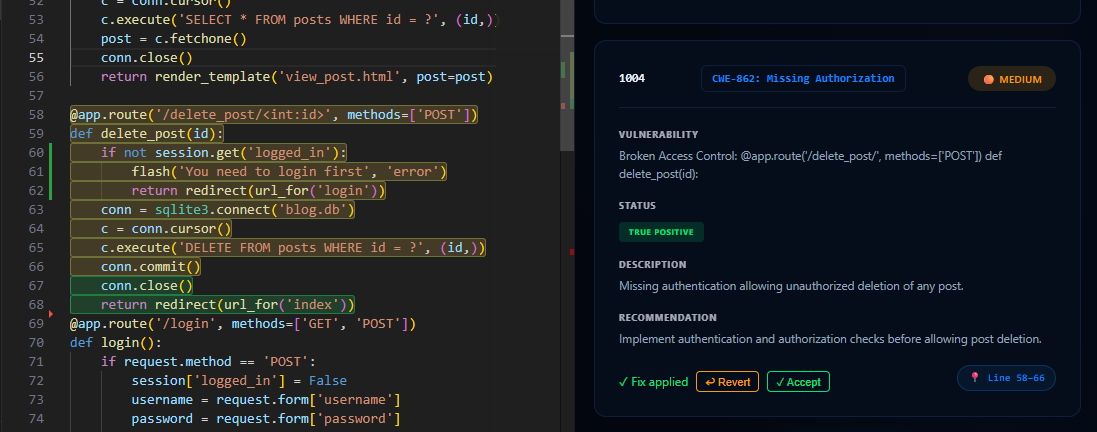
Accept or Revert the Fix
Once the fix is ready, it is automatically applied to the file and the changed lines are highlighted in green. The finding card updates to show two action buttons: Accept — permanently keeps the fix, removes the finding from the list, and clears the highlight; Revert — undoes the fix and restores the original code, bringing the finding back to its original state.