Every Vulnerability Comes With
Its Fix. Automatically.
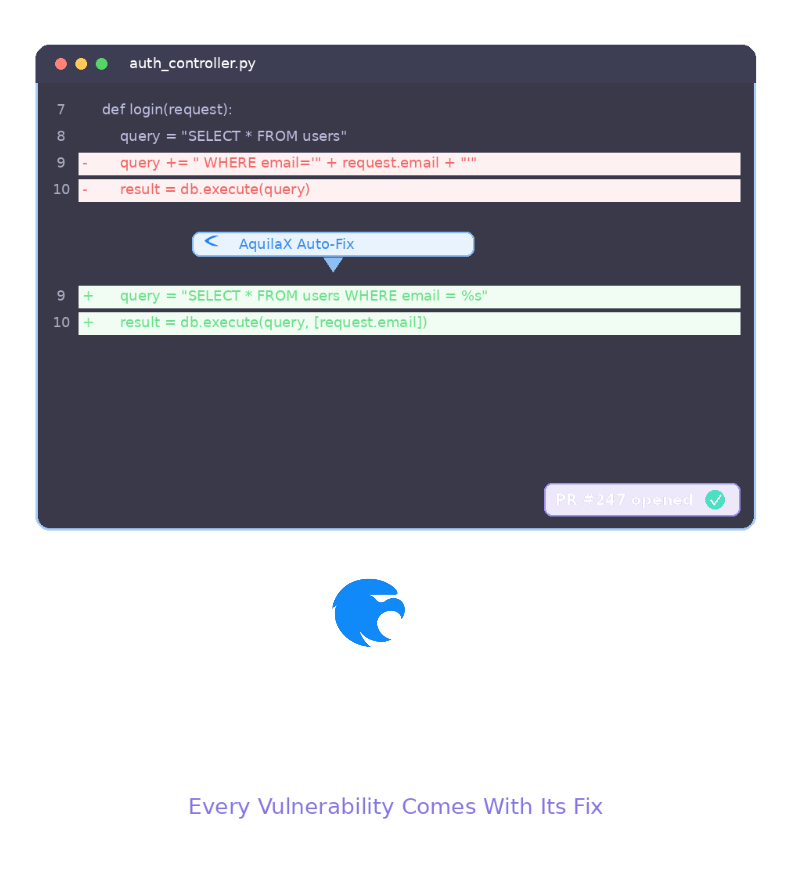
Checkmarx tells you what's wrong. SonarQube gives you a recommendation. AquilaX generates validated fix code specific to your codebase and opens a pull request — automatically.